Conviso AST
Introduction
Scan and protect your codebase with Conviso AST, a security scanner focused on SAST.
Objective
With Conviso AST, you can analyze your source code and consolidate the results in Conviso Platform Vulnerability management module. We utilize a unified security engine featuring Semgrep with Conviso-managed rules, this engine aggregates and deduplicates scan results.
SAST
Currently we support the following languages using Semgrep with Conviso managed rules:
- C#
- Go
- Java
- JavaScript
- Kotlin
- Python
- Typescript
- C / C++
- JSX
- Ruby
- Scala
- Swift
- Rust
- PHP
- Generic
- JSON
Elixir is not yet supported by Semgrep. We use Sobelow, enhanced with Conviso-managed generic Semgrep rules, for Elixir security scans.
How to use Conviso AST?
Scan directly from your terminal with New CLI and combine other capabilities such as:
- Set policies to block the pipeline depending on different criteria;
- Send diff versions of your source code application to later be reviewed by your own security team or - Conviso's (when subscribed to our professional services license).
- Auto-close open vulnerabilities on the platform that are no longer identified during its execution, and can reopen them if they were closed but identified later.
Conviso AST integrates with all the major CI/CD tools in the market, whether on Github Actions, Gitlab, Jenkins, and many others; discover our integrations here.
The analysis results are sent to Conviso Platform, where you can view, prioritize and fix the vulnerabilities found using our Vulnerabilities feature.
How to automatically close resolved vulnerabilities with Conviso AST?
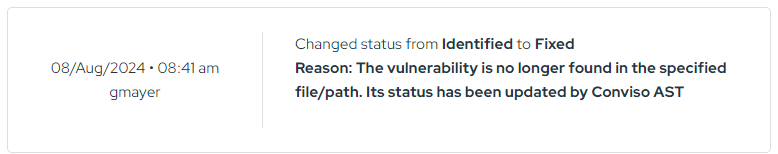
Conviso AST does not fix vulnerabilities in your code. Instead, it can automatically close vulnerabilities in Conviso Platform when they are no longer detected in a new scan.
After fixing the code in your repository, rerun the scan with:
conviso ast run --vulnerability-auto-close
With this option enabled, vulnerabilities not found anymore are automatically moved to a closed status in Conviso Platform. You will see a message indicating that the issue was auto-closed after validation in the new scan.
Dry-Run Mode
The Dry-Run mode lets you run security scans entirely locally, without interacting with the Conviso Platform. It is designed for fast feedback during development—use it in pre-commit hooks, local validation, or CI pipelines where you need results without creating assets or uploading findings.
Key principles
- Local only: All scans run inside Docker containers on your machine.
- No side effects: Nothing is created or uploaded to the Conviso Platform.
- Machine-readable output: Results are printed as JSON to stdout, or to a file you specify.
- Fast: Skips non-essential platform tasks (e.g., technology recovery) to finish as quickly as possible.
SAST Dry-Run
Analyzes source code for vulnerabilities. Without any flags it performs a full scan; use --start-commit and --end-commit to restrict the analysis to a specific commit range—ideal for scanning only what changed in a pull request.
# Full scan
conviso sast dry-run
# Scan only the changes introduced in a PR (base branch → head commit)
conviso sast dry-run --start-commit origin/main --end-commit HEAD
SCA Dry-Run
Scans manifest files (e.g., package-lock.json, Gemfile.lock, requirements.txt) for vulnerable third-party dependencies using osv-scanner.
conviso sca dry-run --repository-dir .
IaC Dry-Run
Checks infrastructure definitions (Terraform, CloudFormation, Kubernetes, and more) for security misconfigurations using Checkov.
conviso iac dry-run --repository-dir ./terraform
AST Dry-Run (Combined)
Runs SAST, SCA, and IaC dry-runs sequentially and returns all results in a single, unified JSON structure.
conviso ast dry-run --start-commit <commit_id>
Command summary
| Command | Scope | Underlying tool |
|---|---|---|
conviso sast dry-run | Source code vulnerabilities (diff-based) | Semgrep + Conviso rules |
conviso sca dry-run | Dependency vulnerabilities | osv-scanner |
conviso iac dry-run | Infrastructure misconfigurations | Checkov |
conviso ast dry-run | All of the above, combined | All of the above |
Support
Should you have any questions or require assistance while using the Conviso Application Security Testing, feel free to contact our dedicated support team.
Contribute to the Docs
Found something outdated or missing? Help us improve the documentation with a quick suggestion or edit.
How to contributeResources
By exploring our content, you'll find resources that will enhance your understanding of the importance of a Security Application Program.
Conviso Blog: Explore our blog, which offers a collection of articles and posts covering a wide range of AppSec topics. The content on the blog is primarily in English.
Conviso's YouTube Channel: Access a wealth of informative videos covering various topics related to AppSec. Please note that the content is primarily in Portuguese.