Risk and Posture Management
Overview
The Risk and Posture Management view combines posture indicators with contextual risk analysis so teams can decide what matters first and track whether security is improving over time.
It is useful for:
- monitoring the overall risk score of your application portfolio;
- tracking how risk changes over time;
- understanding remediation speed through MTTR metrics;
- identifying overdue risk acceptance trends;
- prioritizing vulnerabilities based on business impact, exposure, and data sensitivity.
Main Metrics
The dashboard includes the following key views:
- Overall Risk Score: the current risk score calculated for the selected scope.
- Risk Score Over Time: trend view of how the score changes across the selected period.
- MTTR: average time to remediate vulnerabilities in the current scope.
- MTTR Over Time by Severity: remediation speed split by severity over time.
- Evolution of Vulnerabilities with Risk Accepted: trend view of vulnerabilities accepted on schedule or overdue.

Understanding the Risk Score
The Risk Score provides a quantitative view of how much risk is associated with an asset. It combines asset context with open vulnerability data so teams can prioritize remediation based on real exposure, not just severity labels.
The score is based on four inputs:
- Business Impact: how critical the asset is to the organization.
- Threats: the amount and severity of open vulnerabilities in
Identified,In Progress, orAwaiting Validation. - Attack Surface: whether the asset is internet-facing or internal.
- Data Classification: whether the asset handles sensitive data such as
PIIorPCI.
For the platform's vulnerability status definitions, see Workflow Status.
Requirements
To calculate the Risk Score correctly, the asset should have:
- business impact defined;
- attack surface defined;
- data classification defined;
- open vulnerability data available.
Until the required information is present, the platform may show the asset with incomplete score information.
Formula
RiskScore = round(0.99 * [50 * (BI / 3) + 15 * (T / 10) + 10 * E + 15 * DC], 2)
Variable definitions:
BI= business impact, wherelow = 1,medium = 2,high = 3T= threat level, wherenotification = 0,low = 3,medium = 6,high = 9,critical = 10E= exploitability, whereinternal = 1,internet_facing = 2DC= data classification, whereconfidential,PII, andPCIcontribute1, and others contribute0
Notes:
- the final score is scaled by
0.99; - the result is rounded to two decimal places;
- the maximum score is approximately
99.
Risk Context Prioritization Funnel
The Risk Context Prioritization Funnel complements the Risk Score by helping teams narrow the remediation backlog based on context.
Instead of looking only at severity, the funnel shows how open vulnerabilities are reduced according to filters such as:
- high business impact;
- internet-facing exposure;
- sensitive data handling.
This helps answer a more useful question than "what is the highest severity issue?": which vulnerabilities represent the highest practical risk to the business right now?
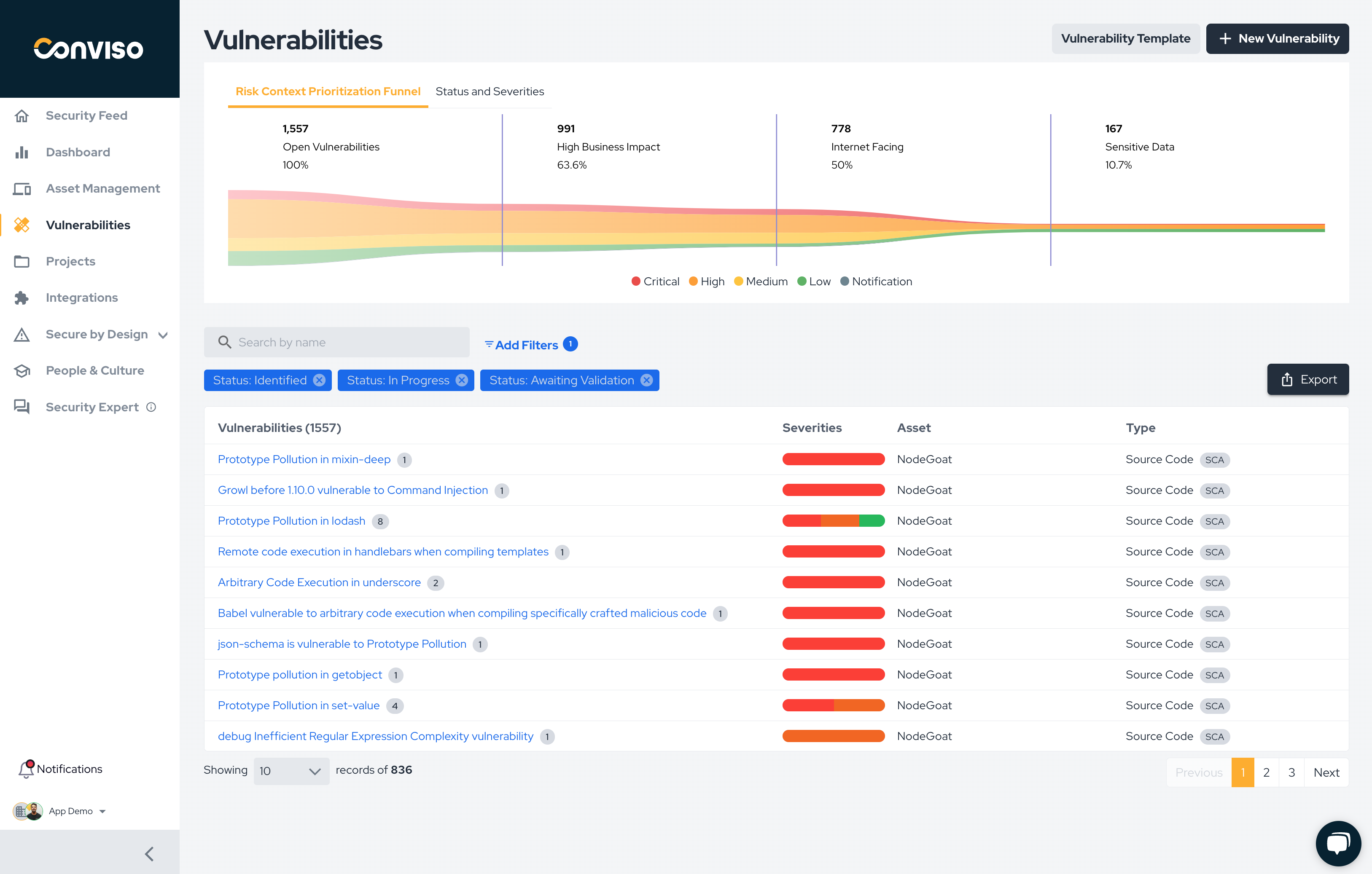
The funnel is especially useful when:
- there is a large backlog of open vulnerabilities;
- teams need to focus on the subset with the highest business relevance;
- severity alone is not enough to define remediation order.
How to Use This View
Use the posture metrics and the contextual funnel together:
- Check whether overall risk and MTTR trends are improving or deteriorating.
- Identify whether risk acceptance and remediation delays are accumulating.
- Use the Risk Score to understand which assets deserve more attention.
- Use the funnel to narrow the vulnerability backlog into the highest-priority subset.
Filters
Use the dashboard filters to adjust the data shown on screen:
- date range;
- assets;
- vulnerability status;
- severity;
- asset tags.
These filters help you focus the posture analysis on a business unit, application group, severity band, or remediation stage.
Contribute to the Docs
Found something outdated or missing? Help us improve the documentation with a quick suggestion or edit.
How to contributeResources
By exploring our content, you'll find resources that will enhance your understanding of the importance of a Security Application Program.
Conviso Blog: Explore our blog, which offers a collection of articles and posts covering a wide range of AppSec topics. The content on the blog is primarily in English.
Conviso's YouTube Channel: Access a wealth of informative videos covering various topics related to AppSec. Please note that the content is primarily in Portuguese.